Master Cybersecurity By Hacking Real Systems
End-to-End!
A cyber-range which gives you realistic hacking experience through advanced target emulation and threat simulation.
Why should you use cyberstruct.io?
cyberstruct.io provides you with high-quality hacking experience through in-depth emulation of the target systems which are hyper-realistic, and thus help you prepare for defending against cyberattacks.
Hyper-realistic target emulation
The target environment built with real infrastructure components running on single or multiple virtual machines just like a production setup of the target
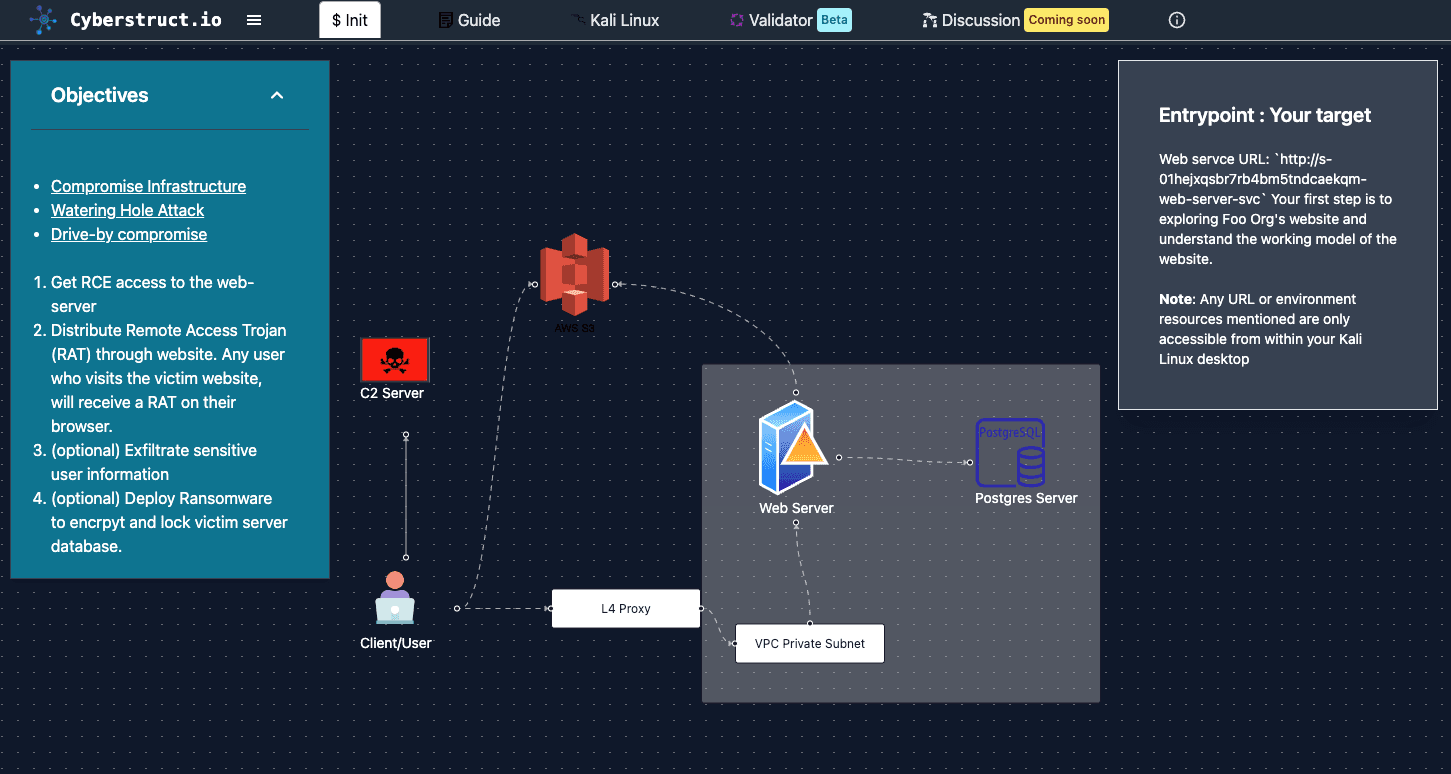
End-to-End Target Infrastructure
cyberstruct.io environments not just provide the target with real vulnerabilities, but also provides all services that are part of the target's infrastructure like CDN, load balancers, AWS services(mocked), DNS, firewall, Kafka, SQL & NoSQL databases, etc
Real-world Attack Surface
End-To-End implementation of the target provides you with multiple attack vectors just like how you would see in real life.
Open/Closed Box Environments
Beginners can take help of the open box environments to get clear understanding of target infrastructure through network visualizations.
CTF on Steroids
The platform emphasizes holistic validation of your tactics and objectives. It goes beyond mere infiltration, ensuring that you successfully accomplish all assigned tasks. These objectives can encompass various elements, such as privilege manipulation, data extraction, and network traversal.
Victim User Emulation
User interaction and behaviour emulation incorporated into the attack environments, creating an immersive experience that challenges participants to think and adapt like true ethical hackers.
CTF
Create or Capture flags placed across the target's network
Progress & Leaderboard
Compete against other hackers
Integrated Console
Kali Linux Desktop
Kali linux desktop along with an integrated terminal directly accessible from the browser console.
Environment Guide
Need help or stuck? get back on track with the help of Guide: a brief walkthrough of the attack/defence.